Sunday, 5. May 2024 Week 18
Needed to create a bootable Debian USB stick for some maintenance on one of my computers.
Here are the steps so I won't have to search for them the next time :-)
- Download the Debian live CD image
- Connect your USB stick and find its device location (/dev/diskX) with:
sudo diskutil list
- If needed unmount your USB stick:
sudo diskutil unmountdisk /dev/diskX
- Write the downloaded image onto the USB stick:
sudo dd if=./debian-live-12.5.0-amd64-standard.iso of=/dev/diskX bs=1m
Wednesday, 24. April 2024 Week 17
Tiny Fragments is a fun little puzzle game made by Daniel Moreno (via)
 Tuesday, 23. April 2024 Week 17
Tuesday, 23. April 2024 Week 17
Interesting article explaining how to test HTML with visual CSS highlighting: Testing HTML with modern CSS (via)
Monday, 15. April 2024 Week 16
In the Print HTTP Headers and Pretty-Print JSON Response post, Susam Pal shows a nice trick to pretty-print JSON output with jq from curl while also showing the HTTP response headers (using stderr):
curl -sSD /dev/stderr https://some-URL-returning-JSON | jq .
Saturday, 13. April 2024 Week 15
Modern Git Commands and Features You Should Be Using — a short article from Martin Heinz about some new-ish (>2018) features in Git, that 'can make your life so much easier'.
TL;DR:
git switch <branchname>git restore --staged <somefile>git restore --source <commit> <somefile>git sparse-checkoutgit worktreegit bisect
Similar post from five years ago: More productive Git
Thursday, 11. April 2024 Week 15
This post from Rachel, reminded me of my own struggle with a Raspberry Pi and time (and yes, I did run into the same DNSSEC problem).
I first tried a RTC shield, but this didn't fully solve all problems.
My workaround in the end is to use two fixed IP addresses in ntp.conf in additon to the usual pool servers.
Thanks ${previous employer} for not changing the IPs of your public NTP servers so far :-)
Wednesday, 10. April 2024 Week 15
As hinted at in my previous post, Solnet is delivering native IPv6 Internet again.
Shortly after 23h on March 26th there was a brief interruption of the Internet uplink and afterwards my router started receiving an IPv6 address again.
My support ticket with Solnet is still unanswered, but at least IPv6 is back :-)
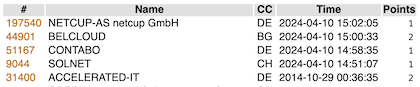
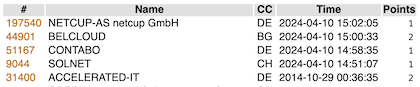
While browsing through the archives I stumbled upon the SixSpotting post from 2014.
Turns out the game is still working and after some failed attempts I managed to remember my account name and log in.
I guess it must look quite strange to see a burst of new checkins after almost 10 years 😄
Sunday, 7. April 2024 Week 14
After following a couple links from the article linked in the previous blogpost, I ended up reading the Website Component Checklist from Mike Sass.
It provides again a lot of inspiration for things to add to my weblog.
What intrigued me today on the list was humans.txt, which is an initiative for knowing the people behing a website.
Thus I've now added the following humans.txt.
100 more things you can do with your personal website — a follow-up to the popular post from last month :-)